Understanding Social Engineering:
What Students Need to Know?
Social engineering involves manipulating or deceiving individuals into performing actions or revealing sensitive information.
Watch out for these three types:

1. DIGITAL THREATS
Phishing:
A type of online scam targeting large organizations (like universities) or groups, often using deceptive emails to trick people into providing personal information.
Spear Phishing:
More specific than phishing, this attack targets an individual, like a particular professor or even yourself, using tailored email scams.
ACTIONS:
STOP! Before clicking any link, opening an attachment, or sharing information, make sure the source is trustworthy. Always stay vigilant to avoid falling for these types of scams.


2. IN-PERSON THREATS
USB Attacks:
This involves plugging in an unfamiliar flash drive, which can install harmful software on your computer when opened.
Shoulder Surfing:
A method where someone attempts to steal your private information by watching you while you use your phone or computer in public.
ACTIONS:
STOP! Before giving in to curiosity when you discover a USB drive or allow another to look over your shoulder while you enter private information.

3. MOBILE/PHONE THREATS
Smishing:
This is phishing via SMS (text messages or social media), where attackers trick you into clicking harmful links or sharing private data.
Vishing:
A voice-based scam, where a caller tries to manipulate you into sharing sensitive information over the phone or through automated systems.
ACTIONS:
STOP! Before clicking on a link in a text/direct message or divulging sensitive information over the phone.

To protect yourself from spam, phishing, smishing, and other forms of Social Engineering attacks, be cautious of unsolicited emails or texts, especially those that ask for personal information, offer jobs, use odd language, or contain suspicious links.
Here Are Some Examples of Things to Be Aware Of:
General Red Flags:
- Unsolicited Messages: Be wary of emails or texts that you didn’t request or expect.
- Requests for Personal Information: Spammers often ask for passwords, social security numbers, or other sensitive data.
- Urgency and Threats: Emails or texts that create a sense of urgency or threaten account suspension are often scams.
- Unusual “From” or “Reply-To” Addresses: Check the sender’s email address carefully for typos or unusual domains.
- Poor Grammar and Spelling: Scam emails often contain grammatical errors and typos.
- Generic Greetings: Emails that don’t address you by name are less likely to be legitimate.
- Suspicious Links: Hover over links to see where they lead, and avoid clicking on links if they seem suspicious.
- Fake Logos or Badges: Scammers sometimes use fake logos or badges to make their emails look legitimate.
- Unusual Attachments: Avoid opening attachments from unknown senders.
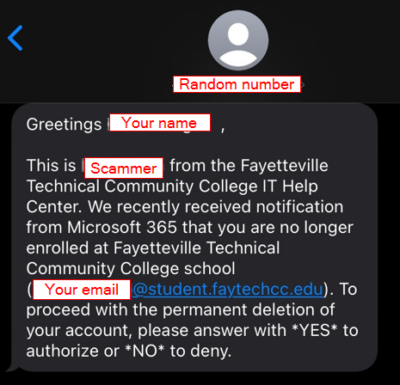
Scam Text Example:
Click on the image below to view it in a larger size.
Specific Phishing/Smishing:
- Fake IT Help Desk Emails: Emails claiming to be from the IT department, requesting account verification or password changes.
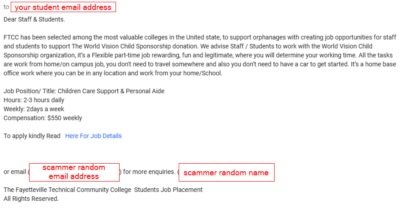
- Fake HR Emails: Emails claiming to be from human resources, often with suspicious links or attachments.
- Fake College/University Emails: Emails claiming to be from the College/University, often with requests for information or money.
- Fake Social Media Requests: Requests from unknown people with the same friends as you, often with links to malicious websites.
- Fake Antivirus Alerts: Pop-ups claiming to detect viruses to sell fake software.
- Fake Copyright Infringement Notices: Emails claiming that your account has been flagged for copyright infringement.
- Fake Email Storage Full Notices: Emails claiming that your email storage is full and asking you to verify your account.
- Fake Email Recovery Emails: Emails claiming that your email account has been compromised and asking you to verify your account.
Scam Email Example:
Click on the image below to view it in a larger size.
What to Do If You Receive a Suspicious Email:

- Don’t Click Links or Open Attachments: If you suspect an email is spam, avoid clicking on any links or opening any attachments.
- Don’t Reply: Spammers often track emails to see if they are active, so avoid replying to suspicious emails.
- Report the Email: Report suspicious emails to your IT department or the relevant authorities.
- Be Wary of Pop-ups: Be cautious of pop-ups that appear on your screen, especially those that claim to detect viruses or ask for personal information.
- Use Strong Passwords: Use strong, unique passwords for all your accounts.
- Enable Two-Factor Authentication: Enable two-factor authentication for your accounts to add an extra layer of security where possible.
- Stay Informed: Keep up-to-date on the latest phishing scams and security threats.